
Hard-coded credentials found in Moxa industrial security appliances, routers (CVE-2025-6950)
Moxa has fixed 5 vulnerabilities in its industrial network security appliances and routers, including a remotely exploitable flaw (CVE-2025-6950) that may result in complete …
China-linked Salt Typhoon hackers attempt to infiltrate European telco
Salt Typhoon, the China-linked APT group that has a penchant for targeting telecommunications companies, has been spotted trying to sneak into yet another one. The intrusion …

Most AI privacy research looks the wrong way
Most research on LLM privacy has focused on the wrong problem, according to a new paper by researchers from Carnegie Mellon University and Northeastern University. The authors …
Why ex-military professionals are a good fit for cybersecurity
After years of working as part of a team, many military veterans look for work that still carries meaning, challenge, and purpose. Cybersecurity offers a new way to serve and …
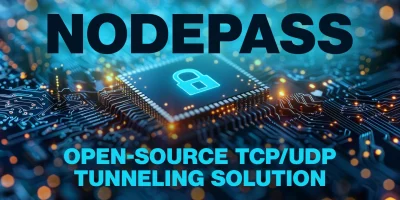
Nodepass: Open-source TCP/UDP tunneling solution
When you think of network tunneling, “lightweight” and “enterprise-grade” rarely appear in the same sentence. NodePass, an open-source project, wants to change that. It’s a …

Why cybersecurity hiring feels so hard right now
In this Help Net Security video, Carol Lee Hobson, CISO at PayNearMe, explores the realities behind the so-called cybersecurity “talent gap.” She explains why the issue is as …

Inside the messy reality of Microsoft 365 management
Most MSPs agree that Microsoft 365 is now the backbone of business operations, but a Syncro survey shows that complexity, incomplete backups, and reactive security continue to …

Week in review: F5 data breach, Microsoft patches three actively exploited zero-days
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Building a healthcare cybersecurity strategy that works In this Help Net …

Hackers used Cisco zero-day to plant rootkits on network switches (CVE-2025-20352)
Threat actors have leveraged a recently patched IOS/IOS XE vulnerability (CVE-2025-20352) to deploy Linux rootkits on vulnerable Cisco network devices. “The operation …

Microsoft revokes 200 certs used to sign malicious Teams installers
By revoking 200 software-signing certificates, Microsoft has hampered the activities of Vanilla Tempest, a ransomware-wielding threat actor that has been targeting …

A new approach to blockchain spam: Local reputation over global rules
Spam has long been a nuisance in blockchain networks, clogging transaction queues and driving up fees. A new research paper from Delft University of Technology introduces a …

Inside healthcare’s quiet cybersecurity breakdown
Hospitals, clinics, and care networks continue to treat cybersecurity as a back-office issue, according to the 2025 Healthcare IT Landscape Report from Omega Systems. Security …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)