Waiting for AI superintelligence? Don’t hold your breath
AI’s impact on systems, security, and decision-making is already permanent. Superintelligence, often referred to as artificial superintelligence (ASI), describes a …

AI’s appetite for data is testing enterprise guardrails
Privacy programs are taking on more operational responsibility across the enterprise. A new Cisco global benchmark study shows expanding mandates, rising investment, and …

Cybersecurity jobs available right now: January 27, 2026
CISO micro1 | USA | Remote – No longer accepting applications As a CISO, you will define the enterprise security vision and implement a zero-trust architecture across …

Claude expands tool connections using MCP
Anthropic has added interactive tool support to its Claude AI platform, a change powered by the open Model Context Protocol (MCP). The update lets users work directly with …

Apple updates AirTag with expanded range and improved findability
Apple has released a new version of its AirTag tracking accessory that extends its connectivity range and improves how items are located. The updated AirTag uses a …

EU opens new investigation into Grok on X
The European Commission has opened a new formal investigation into X under the Digital Services Act over risks linked to the deployment of its AI tool Grok in the EU. …

Poland repels data-wiping malware attack on energy systems
Suspected Russian cyber attackers tried to take down parts of Poland’s energy infrastructure with new data-wiping malware – and failed. According to information shared …
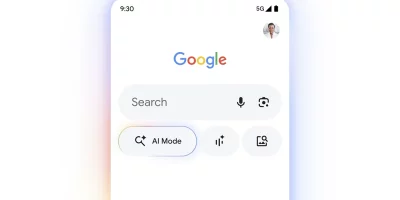
Google ties AI Search to Gmail and Photos, raising new privacy questions
Google is expanding Personal Intelligence into AI Mode in Google Search to deliver more personalized search results. AI Mode can securely connect to your Gmail and Google …

Microsoft Entra ID will auto-enable passkey profiles, synced passkeys
Starting March 2026, Microsoft Entra ID will automatically enable passkey profiles and introduce support for synced passkeys. Passkey profiles move into general availability …
Inside Microsoft’s veteran-to-tech workforce pipeline
The technology workforce is changing, and military veterans are increasingly being recognized as one of the industry’s most valuable and dependable talent pools. In this Help …
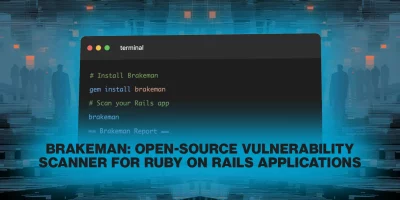
Brakeman: Open-source vulnerability scanner for Ruby on Rails applications
Brakeman is an open-source security scanner used by teams that build applications with Ruby on Rails. The tool focuses on application code and configuration, giving developers …

Incident response lessons learned the hard way
In this Help Net Security video, Ryan Seymour, VP, Consulting and Education at ConnectSecure, shares lessons from more than two decades in cybersecurity incident response. He …
Featured news
Resources
Don't miss
- State-backed phishing attacks targeting military officials and journalists on Signal
- Poland’s energy control systems were breached through exposed VPN access
- CISA orders US federal agencies to replace unsupported edge devices
- Ransomware attackers are exploiting critical SmarterMail vulnerability (CVE-2026-24423)
- February 2026 Patch Tuesday forecast: Lots of OOB love this month