
The unseen side of malware and how to find it
Security teams rely on threat reports to understand what’s out there and to keep their organizations safe. But a new report shows that these reports might only reveal part of …

New infosec products of the week: September 19, 2025
Here’s a look at the most interesting products from the past week, featuring releases from Absolute Security, Catchpoint, Nagomi Security, Neon Cyber, and QuSecure. Absolute …

SonicWall says attackers compromised some firewall configuration backup files
Between attackers exploiting 0-day and n-day vulnerabilities in the company’s firewalls and Secure Mobile Access appliances, SonicWall and its customers have had a tough …

Google fixes actively exploited Chrome zero-day vulnerability (CVE-2025-10585)
Google has released a security update for the Chrome stable channel to fix a zero‑day vulnerability (CVE-2025-10585) reported by its Threat Analysis Group (TAG) on Tuesday. …

LinkedIn now uses your data for AI by default, opt out now!
LinkedIn is making major changes to its User Agreement and Privacy Policy, effective November 3, 2025. Among the most notable updates, the company will now use member data by …

Behind the scenes of cURL with its founder: Releases, updates, and security
In this Help Net Security interview, Daniel Stenberg, lead developer od cURL, discusses how the widely used tool remains secure across billions of devices, from cloud services …
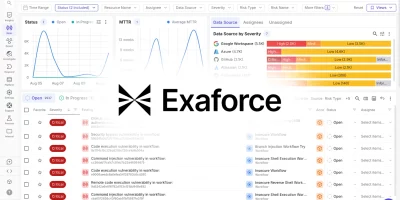
Product showcase: Exaforce – The full lifecycle AI SOC platform
Today’s SOCs face an impossible equation: too much noise, too many gaps, and too few hands. Detection coverage gaps leave companies exposed, false positives overwhelm …

AI made crypto scams far more dangerous
The first half of 2025 saw one of the worst waves of crypto hacks to date, with more than $3.01 billion stolen. AI was a big part of it, making scams easier to run and letting …

Shadow AI is breaking corporate security from within
Cybersecurity leaders know the attack surface has been growing for years, but the latest State of Information Security Report 2025 from IO shows how fast new risks are …

Global hiring risks: What you need to know about identity fraud and screening trends
Hiring new employees has always carried some risk, but that risk is growing in new ways, and identity fraud is becoming more common in the hiring process. HireRight’s 2025 …

Many networking devices are still vulnerable to pixie dust attack
Despite having been discovered and reported in 2014, the vulnerability that allows pixie dust attacks still impacts consumer and SOHO networking equipment around the world, …

Microsoft disrupts the RaccoonO365 Phishing-as-a-Service operation, names alleged leader
Microsoft and Cloudflare have disrupted a Phishing-as-a-Service operation selling the RaccoonO365 kit for stealing Microsoft 365 account credentials. “Using a court …
Featured news
Resources
Don't miss
- State-backed phishing attacks targeting military officials and journalists on Signal
- Poland’s energy control systems were breached through exposed VPN access
- CISA orders US federal agencies to replace unsupported edge devices
- Ransomware attackers are exploiting critical SmarterMail vulnerability (CVE-2026-24423)
- February 2026 Patch Tuesday forecast: Lots of OOB love this month