
EU’s Chat Control could put government monitoring inside robots
Cybersecurity debates around surveillance usually stay inside screens. A new academic study argues that this boundary no longer holds when communication laws extend into …

Downtime pushes resilience planning into security operations
CISOs describe a shift in how they define success. New research from Absolute Security shows broad agreement that resilience outweighs security goals centered on prevention …

Week in review: PoC for Trend Micro Apex Central RCE released, Patch Tuesday forecast
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Pharma’s most underestimated cyber risk isn’t a breach Chirag Shah, Global …

European Commission opens consultation on EU digital ecosystems
The European Commission has opened a public call for evidence on European open digital ecosystems, a step toward a planned Communication that will examine the role of open …

January 2026 Patch Tuesday forecast: And so it continues
Welcome to a new year of my Patch Tuesday forecast blog where I provide a summary of Microsoft and other vendor’s security patch activity (and reported issues) for the month, …

How AI agents are turning security inside-out
AppSec teams have spent the last decade hardening externally facing applications, API security, software supply chain risk, CI/CD controls, and cloud-native attack paths. But …
Product showcase: TrackerControl lets Android users see who’s tracking them
TrackerControl is an open-source Android application designed to give users visibility into and control over the hidden data within mobile apps. Many apps routinely …
Security teams are paying more attention to the energy cost of detection
Security teams spend a lot of time explaining why detection systems need more compute. Cloud bills rise, models retrain more often, and new analytics pipelines get added to …

Wi-Fi evolution tightens focus on access control
Wi-Fi networks are taking on heavier workloads, more devices, and higher expectations from users who assume constant access everywhere. A new Wireless Broadband Alliance …
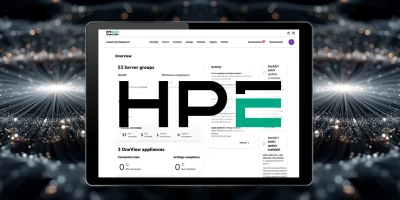
Recently fixed HPE OneView flaw is being exploited (CVE-2025-37164)
An unauthenticated remote code execution vulnerability (CVE-2025-37164) affecting certain versions of HPE OneView is being leveraged by attackers, CISA confirmed by adding the …

PoC released for unauthenticated RCE in Trend Micro Apex Central (CVE-2025-69258)
Trend Micro has released a critical patch fixing several remotely exploitable vulnerabilities in Apex Central (on-premise), including a flaw (CVE-2025-69258) that may allow …

IPFire update brings new network and security features to firewall deployments
Security and operations teams often work with firewall platforms that require frequent tuning or upgrades to meet evolving network demands. IPFire has released its 2.29 Core …
Featured news
Resources
Don't miss
- Researcher drops two more Microsoft Defender zero-days, all three now exploited in the wild
- Workplace stress in 2026 is still worse than before the pandemic
- NIST admits defeat on NVD backlog, will enrich only highest-risk CVEs going forward
- Anthropic releases Claude Opus 4.7 with automated cybersecurity safeguards
- Cargo theft malware actor spent a month inside a decoy network before researchers pulled the plug