
Cybersecurity spending keeps rising, so why is business impact still hard to explain?
Cybersecurity budgets keep climbing, but many security leaders still struggle to explain what that spending delivers to the business. A new study by Expel examines that …

The NSA lays out the first steps for zero trust adoption
Security pros often say that zero trust sounds straightforward until they try to apply it across real systems, real users, and real data. Many organizations are still sorting …

Webinar: Beyond the Quadrant: An Analyst’s Guide to Evaluating Email Security in 2026
Join former Gartner analyst Ravisha Chugh and Abnormal’s Director of Product Marketing, Lane Billings, on January 20th for an exclusive insider look at how email security …
Anthropic backs Python Software Foundation security work with $1.5 million
Anthropic has signed a two-year partnership with the Python Software Foundation (PSF), committing a total of $1.5 million to support the foundation’s work, with a focus on …

CISO Assistant: Open-source cybersecurity management and GRC
CISO Assistant is an open-source governance, risk, and compliance (GRC) platform designed to help security teams document risks, controls, and framework alignment in a …
Firmware scanning time, cost, and where teams run EMBA
Security teams that deal with connected devices often end up running long firmware scans overnight, checking progress in the morning, and trying to explain to colleagues why a …

How AI image tools can be tricked into making political propaganda
A single image can shift public opinion faster than a long post. Text to image systems can be pushed to create misleading political visuals, even when safety filters are in …

Product showcase: Orbot – Tor VPN for iOS
Orbot for iOS is a free, open-source networking tool that routes supported app traffic through the Tor network. Developed by the Guardian Project, it is intended for users who …
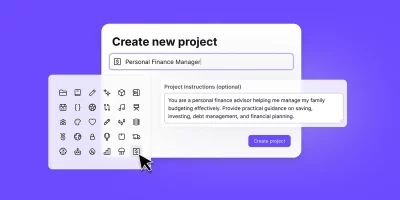
Proton expands Lumo AI assistant with encrypted, project-based workspaces
Lumo is Proton’s AI assistant, built with a focus on privacy and user control. It runs on Proton’s infrastructure and is designed so conversations are not used to train models …

Wine 11 brings major architectural work, synchronization changes, 600+ bug fixes
Wine, originally short for “Wine Is Not an Emulator,” is a compatibility layer that allows Windows applications to run natively on POSIX-compliant operating systems, including …

AuraInspector: Open-source tool to audit Salesforce Aura access control misconfigurations
Google and its Mandiant threat intelligence unit have released AuraInspector, an open-source tool aimed at auditing data access paths in Salesforce Experience Cloud …

Browser-in-the-Browser phishing is on the rise: Here’s how to spot it
Browser-in-the-Browser (BitB) phishing attacks are on the rise, with attackers reviving and refining the technique to bypass user skepticism and traditional security controls. …
Featured news
Resources
Don't miss
- Cargo theft malware actor spent a month inside a decoy network before researchers pulled the plug
- EU cybersecurity standards are at risk if supplier ban passes
- What the EU AI Act requires for AI agent logging
- Webinar: The IT Leader’s Guide to AI Governance
- OpenAI expands its cyber defense program with GPT-5.4-Cyber for vetted researchers