
Manufacturing is becoming a test bed for ransomware shifts
Manufacturing leaders may feel that ransomware risk has settled, but new data shows the threat is shifting in ways that require attention, according to a Sophos report. A …

Week in review: 40 open-source tools securing the stack, invisible IT to be the next workplace priority
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: 40 open-source tools redefining how security teams secure the stack Open …

What 35 years of privacy law say about the state of data protection
Privacy laws have expanded around the world, and security leaders now work within a crowded field of requirements. New research shows that these laws provide stronger rights …

LLM privacy policies keep getting longer, denser, and nearly impossible to decode
People expect privacy policies to explain what happens to their data. What users get instead is a growing wall of text that feels harder to read each year. In a new study, …

Ransomware keeps widening its reach
Ransomware keeps shifting into new territory, pulling in victims from sectors and regions that once saw fewer attacks. The latest Global Threat Briefing for H2 2025 from …

Uneven regulatory demands expose gaps in mobile security
Mobile networks carry a great deal of the world’s digital activity, which makes operators a frequent target for attacks. A study released by the GSMA shows that operators …

New infosec products of the week: December 12, 2025
Here’s a look at the most interesting products from the past week, featuring releases from Apptega, Backslash Security, BigID, Black Kite, Bugcrowd, NinjaOne, Nudge Security, …

40 open-source tools redefining how security teams secure the stack
Open source security software has become a key way for teams to get flexibility, transparency, and capability without licensing costs. The free tools in this roundup address …

LLM vulnerability patching skills remain limited
Security teams are wondering whether LLMs can help speed up patching. A new study tests that idea and shows where the tools hold up and where they fall short. The researchers …

Password habits are changing, and the data shows how far we’ve come
In this Help Net Security video, Andréanne Bergeron, Security Researcher at Flare, explains how changes in user habits, policy shifts, and new tools have shaped password …
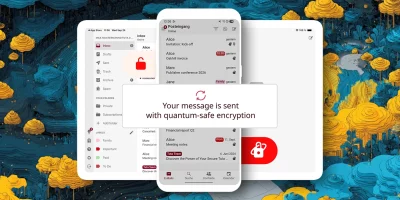
Product showcase: Tuta – secure, encrypted, private email
Tuta, formerly known as Tutanota, is built for anyone who wants email that stays private. Instead of treating encryption like a bonus feature, the service encrypts almost …

Teamwork is failing in slow motion and security feels it
Security leaders often track threats in code, networks, and policies. But a quieter risk is taking shape in the everyday work of teams. Collaboration is getting harder even as …
Featured news
Resources
Don't miss
- State-backed phishing attacks targeting military officials and journalists on Signal
- Poland’s energy control systems were breached through exposed VPN access
- CISA orders US federal agencies to replace unsupported edge devices
- Ransomware attackers are exploiting critical SmarterMail vulnerability (CVE-2026-24423)
- February 2026 Patch Tuesday forecast: Lots of OOB love this month