
How compliance teams can turn AI risk into opportunity
AI is moving faster than regulation, and that creates opportunities and risks for compliance teams. While governments work on new rules, businesses cannot sit back and wait. …

Hottest cybersecurity open-source tools of the month: August 2025
This month’s roundup features exceptional open-source cybersecurity tools that are gaining attention for strengthening security across various environments. Buttercup: …
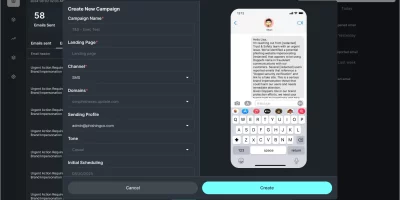
What CISOs can learn from Doppel’s new AI-driven social engineering simulation
Doppel has introduced a new product called Doppel Simulation, which expands its platform for defending against social engineering. The tool uses autonomous AI agents to create …

Social media apps that aggressively harvest user data
Both domestic and foreign technology companies collect vast amounts of Americans’ personal data through mobile applications, according to Incogni. Some apps leverage data for …

NetScaler ADC/Gateway zero-day exploited by attackers (CVE-2025-7775) – updated!
Three new vulnerabilities affecting (Citrix) NetScaler application delivery controller (ADC) and Gateway devices have been made public, one of which (CVE-2025-7775) has been …

Git vulnerability leading to RCE is being exploited by attackers (CVE-2025-48384)
CVE-2025-48384, a recently patched vulnerability in the popular distributed revision control system Git, is being exploited by attackers. Details about the attacks are not …

Protecting farms from hackers: A Q&A with John Deere’s Deputy CISO
Agriculture is a connected, software-driven industry where cybersecurity is just as essential as tractors and harvesters. From embedded hardware in smart fleets to defending …
The energy sector has no time to wait for the next cyberattack
The energy sector remains a major target for cybercriminals. Beyond disrupting daily routines, a power outage can undermine economic stability and public safety. Rising demand …

LLMs at the edge: Rethinking how IoT devices talk and act
Anyone who has set up a smart home knows the routine: one app to dim the lights, another to adjust the thermostat, and a voice assistant that only understands exact phrasing. …

How to build a secure AI culture without shutting people down
In this Help Net Security video, Michael Burch, Director of Application Security at Security Journey, explains how organizations can build a secure AI culture. He highlights …

Cybersecurity jobs available right now: August 26, 2025
Sr. Cybersecurity Analyst Aecon Group Inc. | USA | On-site – No longer accepting applications As a Sr. Cybersecurity Analyst, you will lead cybersecurity and compliance …

ScreenConnect admins targeted with spoofed login alerts
ScreenConnect cloud administrators across all region and industries are being targeted with fake email alerts warning about a potentially suspicious login event. The goal of …
Featured news
Resources
Don't miss
- 29 million leaked secrets in 2025: Why AI agents credentials are out of control
- Hackers hijacked CPUID downloads, served STX RAT to victims
- Adobe issues emergency fix for Acrobat Reader flaw exploited in the wild (CVE-2026-34621)
- Fixing vulnerability data quality requires fixing the architecture first
- ZeroID: Open-source identity platform for autonomous AI agents