
OT security needs continuous operations, not one-time fixes
Cyberattacks keep hitting the OT systems that critical infrastructure operators run, according to new research from Forrester. In a survey of 262 OT security decision-makers, …

Cybersecurity jobs available right now: September 16, 2025
CISO Haier Europe | Italy | On-site – No longer accepting applications As a CISO, you will develop an information security strategy aligned with organizational …

Phishing campaign targets Rust developers
Developers publishing crates (binaries and libraries written in Rust) on crates.io, Rust’s main public package registry, have been targeted with emails echoing the recent npm …

Most enterprise AI use is invisible to security teams
Most enterprise AI activity is happening without the knowledge of IT and security teams. According to Lanai, 89% of AI use inside organizations goes unseen, creating risks …
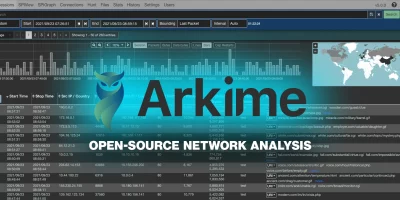
Arkime: Open-source network analysis and packet capture system
Arkime is an open-source system for large-scale network analysis and packet capture. It works with your existing security tools to store and index network traffic in standard …

What could a secure 6G network look like?
The official standards for 6G are set to be announced by the end of 2029. While the industry is moving towards consensus around how the 6G network will be built, it also needs …

Why neglected assets are the hidden threat attackers love to find
In this Help Net Security video, Tim Chase, Tech Evangelist at Orca Security, explores one of the most overlooked cybersecurity risks: neglected assets. From forgotten cloud …

Static feeds leave intelligence teams reacting to irrelevant or late data
Boards and executives are not asking for another feed of indicators. They want to know whether their organization is being targeted, how exposed they are, and what steps need …

Week in review: Salesloft Drift breach investigation results, malicious GitHub Desktop installers
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Salesloft Drift data breach: Investigation reveals how attackers got in The …

HybridPetya: (Proof-of-concept?) ransomware can bypass UEFI Secure Boot
ESET researchers have discovered HybridPetya, a bootkit-and-ransomware combo that’s a copycat of the infamous Petya/NotPetya malware, augmented with the capability of …

CISA looks to partners to shore up the future of the CVE Program
The US Cybersecurity and Infrastructure Security Agency (CISA) has affirmed its continuing support for the Common Vulnerabilities and Exposures (CVE) program. “If we …
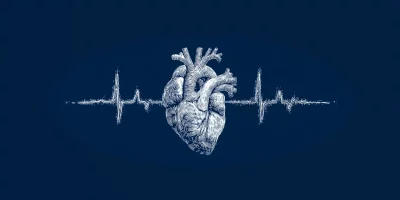
Your heartbeat could reveal your identity, even in anonymized datasets
A new study has found that electrocardiogram (ECG) signals, often shared publicly for medical research, can be linked back to individuals. Researchers were able to re-identify …
Featured news
Resources
Don't miss
- New Mirai variants target routers and DVRs in parallel campaigns
- Progress Software fixes sneaky WAF bypass vulnerability (CVE-2026-21876)
- PentAGI: Open-source autonomous AI penetration testing system
- CISA flags another Cisco Catalyst SD-WAN Manager bug as exploited (CVE-2026-20133)
- Researchers build an encrypted routing layer for private AI inference