quantum computing

Apple makes its quantum-resistant encryption open source
Apple has published its post-quantum cryptography implementations in corecrypto, together with mathematical proofs and verification tools for independent expert evaluation, …
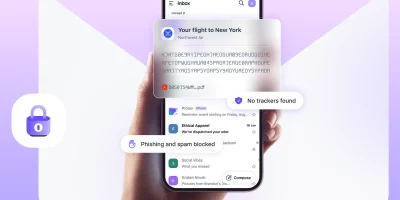
Proton Mail brings quantum-safe email encryption to all accounts
Post-quantum protection is now available as an optional feature in Proton Mail across all plans, including the free tier. How post-quantum protection works Once enabled, …

Cloudflare moves up its post-quantum deadline as researchers narrow the path to Q-Day
Cloudflare announced it is targeting 2029 to complete post-quantum security across its entire product suite, including post-quantum authentication. The company is following a …

Crypto industry may be running out of time to prepare for quantum attacks
Google’s latest research suggests the cryptocurrency industry may have less time than expected to prepare for quantum computing. In a whitepaper, Google examines risks to …

Google races to secure encryption before quantum threats arrive
Google is preparing for the quantum era, a turning point in digital security, with a 2029 timeline for post-quantum cryptography (PQC) migration. Security professionals warn …

Quantum threats are already active and the defense response remains fragmented
Enterprises are moving toward post-quantum security at uneven speeds, and the gap between organizations that have built crypto-agility into their infrastructure and those that …

Certificate lifespans are shrinking and most organizations aren’t ready
The push for shorter TLS certificate lifespans has been building for years. It started with Google’s internal push toward 90-day certificates, which gained traction inside the …

Microsoft adds domain libraries and Copilot integration to the quantum development kit
The Microsoft Quantum Development Kit (QDK) is an open-source toolkit that runs on laptops and in common development environments. It includes code, simulators, libraries, and …

Quantum security is turning into a supply chain problem
Supplier onboarding, invoice processing, and procurement platforms run on encrypted data flows that were built for long-term trust. In many organizations, that trust still …

Your encrypted data is already being stolen
Quantum computing is often treated as a distant, theoretical cybersecurity issue. According to Ronit Ghose, Global Head, Future of Finance of Citi Institute, that mindset is …

A new framework helps banks sort urgent post-quantum crypto work from the rest
Financial institutions now have a concrete method for deciding where post-quantum cryptography belongs on their security roadmaps. New research coordinated by Europol sets out …

What insurers expect from cyber risk in 2026
Technology shifts, policy decisions, and attacker behavior are changing at the same time, and their effects increasingly overlap. Insurers, brokers, and security teams are …
Featured news
Resources
Don't miss
- Windows Netlogon RCE exploited, domain controllers at risk (CVE-2026-41089)
- How NIST fumbled management of the National Vulnerability Database
- Hackers are exploiting Palo Alto GlobalProtect VPN authentication bypass (CVE-2026-0257)
- NVIDIA goes open source with a big batch of physical AI agent tools
- Data discovery gaps that catch enterprises off guard