
Websites can spy on user activity by analyzing SSD behavior
Websites have spent years collecting information about visitors through browser fingerprinting, tracking scripts, and other techniques designed to identify devices and monitor …
Product showcase: TotalAV helps iOS users clean up their digital mess
TotalAV Mobile Security helps protect devices from malicious websites, SMS scams, unsafe public Wi-Fi networks, and exposed credentials. The app is available for Windows, …
Turns out the C-suite loves shadow AI
Senior decision-makers are the heaviest users of unapproved AI tools, and they continue using them despite being aware of the security and privacy risks linked to shadow AI, …

The end of unencrypted Discord calls is here
Discord has protected voice and video calls in DMs, group DMs, voice channels, and Go Live streams with end-to-end encryption (E2EE) by default. The company began …
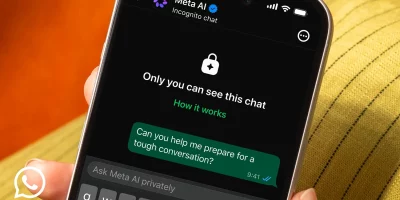
WhatsApp adds Incognito Chat for private Meta AI conversations
The company launched Incognito Chat with Meta AI, a feature that lets users hold AI conversations the platform itself cannot read. The rollout will reach WhatsApp and the …
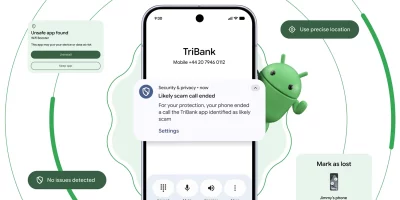
Android pushes new scam, theft, and AI protections in 2026 update wave
Phone scammers spoofing bank caller IDs have driven an estimated $980 million in annual losses worldwide, according to Europol. Android’s 2026 security roadmap takes …

General Motors to pay $12.75 million over driver data sales
General Motors has agreed to a $12.75 million settlement with California over allegations that it unlawfully sold drivers’ location and behavioral data to brokers, …

Škoda confirms unauthorized access to its online shop
Car manufacturer Škoda discovered that attackers had exploited a vulnerability in its online shop software and gained temporary unauthorized access to the system. What …

The hidden smart fridge risks that emerge years after purchase
Household refrigerators are built to last more than a decade. The software, cloud services, and mobile apps that control them are not. A new analysis from Erik Buchmann at …

Instagram messaging encryption removed, and privacy advocates are pushing back
After introducing optional end-to-end encrypted messaging in 2023, Instagram announced in March 2026 that encryption for direct messages would be discontinued, and the feature …

Google is turning Android Studio into a policy watchdog
Google has expanded Play Policy Insights in Android Studio to help developers catch policy issues while coding, including warnings for common problems such as missing login …

Roblox chat moderation gets bypassed by leet speak and code words
Roblox runs an automated chat filter at the scale of billions of messages per day. An independent audit of about two million chat messages from four of the platform’s …
Featured news
Resources
Don't miss
- Dutch police disrupts botnet composed of 17 million devices
- New infostealer reaches enterprise devices through FortiClient EMS vulnerability
- LinkedIn-themed phishing abuses Adobe’s A/B testing platform
- The behavioral signals that sharpen Trojan malware detection
- Zapier exploit chain shows how known anti-patterns compose into critical risk