cybersecurity
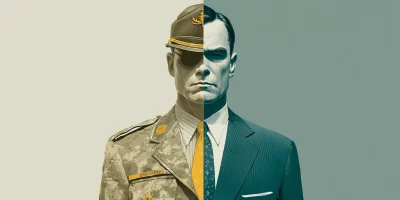
Inside Microsoft’s veteran-to-tech workforce pipeline
The technology workforce is changing, and military veterans are increasingly being recognized as one of the industry’s most valuable and dependable talent pools. In this Help …

Incident response lessons learned the hard way
In this Help Net Security video, Ryan Seymour, VP, Consulting and Education at ConnectSecure, shares lessons from more than two decades in cybersecurity incident response. He …

Exposed training apps are showing up in active cloud attacks
Security teams often spin up vulnerable applications for demos, training, or internal testing. A recent Pentera research report documents how those environments are being left …

Unbounded AI use can break your systems
In this Help Net Security video, James Wickett, CEO of DryRun Security, explains cyber risks many teams underestimate as they add AI to products. He focuses on how fast LLM …

The internet’s oldest trust mechanism is still one of its weakest links
Attackers continue to rely on domain names as an entry point into enterprise systems. A CSC domain security study finds that large organizations leave this part of their …

macOS Tahoe improves privacy and communication safety
macOS Tahoe privacy and security features focus on screening unwanted contact, limiting tracking, and keeping more decisions on the device. Most updates run quietly in the …

Pro-Russian hacktivist campaigns continue against UK organizations
The UK’s National Cyber Security Centre reports ongoing cyber operations by Russian-aligned hacktivist groups targeting organizations in the UK and abroad. NoName057(16) …

Cybercriminals speak the language young people trust
Criminal groups actively recruit, train, and retain people in structured ways. They move fast, pay in crypto, and place no weight on age. Young people are dealing with a new …

Bandit: Open-source tool designed to find security issues in Python code
Bandit is an open-source tool that scans Python source code for security issues that show up in everyday development. Many security teams and developers use it as a quick way …

The 2026 State of Pentesting: Why delivery and follow-through matter more than ever
Penetration testing has evolved significantly over the past several years. While uncovering exploitable vulnerabilities remains the core goal, the real differentiator today is …

Security leaders push for continuous controls as audits stay manual
Security teams say they want real-time insight into controls, but still rely on periodic checks that trail daily operations. New RegScale research shows how wide that gap …

Product showcase: PrivacyHawk for iOS helps users track and remove personal data from data brokers
Every interaction online, from signing up for a newsletter to making a purchase, leaves a trace. These traces are collected by data brokers and resold to advertisers, …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)