authentication

Social data puts user passwords at risk in unexpected ways
Many CISOs already assume that social media creates new openings for password guessing, but new research helps show what that risk looks like in practice. The findings reveal …

Why password management defines PCI DSS success
Most CISOs spend their days dealing with noisy dashboards and vendor pitches that all promise a shortcut to compliance. It can be overwhelming to sort out what matters. When …

The identity mess your customers feel before you do
Customer identity has become one of the most brittle parts of the enterprise security stack. Teams know authentication matters, but organizations keep using methods that …

Research shows identity document checks are missing key signals
Most CISOs spend their time thinking about account takeover and phishing, but identity document fraud is becoming a tougher challenge. A new systematic review shows how …

Is your password manager truly GDPR compliant?
Passwords sit at the core of every critical system, but many organizations still overlook how fragile their password workflows can be. When something goes wrong, security …
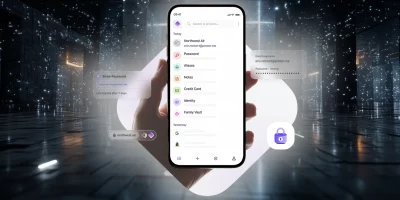
Product showcase: Proton Pass, a password manager with identity protection
Managing passwords can be a real headache, and it’s still common to fall back on reusing them or storing them in a browser without much protection. Proton Pass, built by the …

Wi-Fi signals may hold the key to touchless access control
Imagine walking into a secure building where the door unlocks the moment your hand hovers near it. No keycards, no PINs, no fingerprints. Instead, the system identifies you by …

Passwordless adoption moves from hype to habit
With the average person juggling more than 300 credentials and credential abuse still the top attack vector, the password’s decline is long overdue. Across every major sector, …

WhatsApp now lets you secure chat backups with passkeys
Messaging service WhatsApp is launching passkey-encrypted chat backups for iOS and Android, allowing users to encrypt their stored message history using their face, …

Can your earbuds recognize you? Researchers are working on it
Biometric authentication has moved from fingerprints to voices to facial scans, but a team of researchers believes the next step could be inside the ear. New research explores …

For blind people, staying safe online means working around the tools designed to help
Blind and low-vision users face the same password challenges as everyone else, but the tools meant to make security easier often end up getting in the way. A study from the …

The password problem we keep pretending to fix
Experts across industries say they are still losing ground against identity-related breaches, even after years of investment in stronger access controls, according to RSA. …
Featured news
Resources
Don't miss
- State-backed phishing attacks targeting military officials and journalists on Signal
- Poland’s energy control systems were breached through exposed VPN access
- CISA orders US federal agencies to replace unsupported edge devices
- Ransomware attackers are exploiting critical SmarterMail vulnerability (CVE-2026-24423)
- February 2026 Patch Tuesday forecast: Lots of OOB love this month