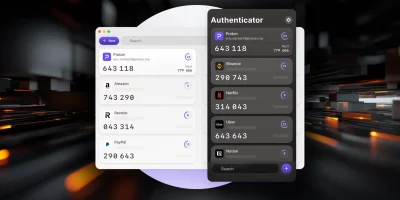
Product showcase: Proton Authenticator is an end-to-end encrypted, open source 2FA app
Proton Authenticator is a free and open-source two-factor authentication (2FA) app that generates time-based one-time passwords (TOTP) to help secure online accounts. It is …

After Shai-Hulud, GitHub tightens npm publishing security
Attackers are constantly finding ways to take over accounts and push malicious packages to the npm registry, the (GitHub-operated) online repository for JavaScript and Node.js …

Aegis Authenticator: Free, open-source 2FA app for Android
Aegis Authenticator is an open-source 2FA app for Android that helps you manage login codes for your online accounts. The app features strong encryption and the ability to …

If you think you’re immune to phishing attempts, you’re wrong!
Security consultant Troy Hunt, the creator of the Have I Been Pwned (HIBP) service, has revealed that he got tricked by a clever phishing email, and that the attacker gained …

Using Authy? Beware of impending phishing attempts
Do you use Authy for your multi-factor authentication needs? If you do, you should keep an eye out for phishing attempts, as well as implement defenses against SIM swapping …

Google Authenticator updated, finally allows syncing of 2FA codes
Google has updated Google Authenticator, its mobile authenticator app for delivering time-based one-time authentication codes, and now allows users to sync (effectively: back …

GitHub to introduce mandatory 2FA authentication starting March 13
Starting March 13, GitHub will gradually introduce the 2FA enrollment requirement to groups of developers and administrators, beginning with smaller groups. This measured …

Twitter will start charging users for SMS-based 2FA option
Twitter has announced that starting with March 20, users who don’t pay the Twitter Blue subscription will no longer be able to use the SMS-based two-factor …

Apple delivers belated zero-day patch for iOS v12 (CVE-2022-42856)
Apple has released security updates for macOS, iOS, iPadOS and watchOS, patching – among other things – a type confusion flaw in the WebKit component …

CircleCI breach post-mortem: Attackers got in by stealing engineer’s session cookie
The attackers who pulled off the recent breach of continuous integration and continuous delivery (CI/CD) platform maker CircleCI got in by compromising an engineer’s …

Apple unveils end-to-end encryption for iCloud backup, Photos, etc.
Apple is expanding end-to-end encryption options for users and finally offering E2EE for their iCloud backup. Advanced Data Protection for iCloud “iCloud already …

2FA, 3FA, MFA… What does it all mean?
Simply put, authentication is the act of proving you are who you say you are. To gain access to protected information, systems or locations, the user must prove their identity …
Featured news
Resources
Don't miss
- Coinflow CISO on crypto payments security under AI pressure
- Vigolium: Open-source vulnerability scanner
- Anthropic: Claude Mythos identified 10,000+ software flaws
- Actively exploited Trend Micro Apex One flaw gets CISA warning (CVE-2026-34926)
- High-severity SharePoint RCE bug patched by Microsoft (CVE-2026-45659)