Help Net Security

More than half of public vulnerabilities bypass leading WAFs
Miggo Security has released a new report that examines how web application firewalls are used across real-world security programs. The research outlines the role WAFs play as …

How exposure management changes cyber defense
In this Help Net Security video, Larry Slusser, VP of Strategy at SixMap, explains why endpoint detection and response is only part of the security story. Drawing on his work …

Week in review: 40 open-source tools securing the stack, invisible IT to be the next workplace priority
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: 40 open-source tools redefining how security teams secure the stack Open …

Password habits are changing, and the data shows how far we’ve come
In this Help Net Security video, Andréanne Bergeron, Security Researcher at Flare, explains how changes in user habits, policy shifts, and new tools have shaped password …
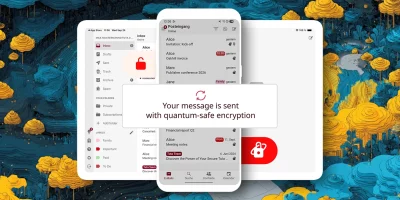
Product showcase: Tuta – secure, encrypted, private email
Tuta, formerly known as Tutanota, is built for anyone who wants email that stays private. Instead of treating encryption like a bonus feature, the service encrypts almost …

The simple shift that turns threat intel from noise into real insight
In this Help Net Security video, Alankrit Chona, CTO at Simbian, explains how security teams can put threat intelligence to work in a way that supports detection, response, …

Download: Evaluating Password Monitoring Vendors
Organizations using Active Directory must update their password policies to block and detect compromised passwords. However, comparing vendors in this area can be challenging. …

December 2025 Patch Tuesday forecast: And it’s a wrap
It’s hard to believe that we’re in December of 2025 already and the end of the year is fast approaching. Looking back on the year, there are two major items that really stand …

Week in review: React, Node.js flaw patched, ransomware intrusion exposes espionage foothold
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Creative cybersecurity strategies for resource-constrained institutions In …

What security leaders should watch for when companies buy or sell a business
In this Help Net Security video, Lane Sullivan, SVP, CISO and Strategy Officer at Concentric AI, explains what security leaders should think about during mergers, …

Product showcase: UserLock IAM for Active Directory
UserLock brings modern identity and access management (IAM) to Active Directory, adding granular multi-factor authentication (MFA), contextual access controls, single sign-on …

What zero trust looks like when you build it step by step
In this Help Net Security video, Jonathan Edwards, Managing Director at KeyData Cyber, walks us through what practical zero trust adoption looks like in stages. He explains …
Featured news
Resources
Don't miss
- State-backed phishing attacks targeting military officials and journalists on Signal
- Poland’s energy control systems were breached through exposed VPN access
- CISA orders US federal agencies to replace unsupported edge devices
- Ransomware attackers are exploiting critical SmarterMail vulnerability (CVE-2026-24423)
- February 2026 Patch Tuesday forecast: Lots of OOB love this month