Cybercriminals select insiders to attack telecom providers
Cybercriminals are using insiders to gain access to telecommunications networks and subscriber data, according to Kaspersky Lab. In addition, these criminals are also recruiting disillusioned employees through underground channels and blackmailing staff using compromising information gathered from open sources.

Telecommunications providers are a top target for cyber-attacks. They operate and manage the world’s networks, voice and data transmissions and store vast amounts of sensitive data, and this makes them a highly attractive target for cybercriminals in search of financial gain, nation-state sponsored actors launching targeted attacks and their competitors.
To achieve their goals, cybercriminals often use insiders as part of their malicious ‘toolset,’ in order to help them breach the perimeter of a telecommunications company and perpetrate their crimes. New research by Kaspersky Lab and B2B International reveals that 28 percent of all cyber-attacks and 38 percent of targeted attacks now involve malicious activity by insiders. The intelligence report examines popular ways of involving insiders in telecom-related criminal schemes and gives examples of how insiders are used.
Compromising employees
According to Kaspersky Lab researchers, attackers engage or entrap telecom employees in the following ways:
- Using publically available or previously stolen data sources to find compromising information on employees of the company they want to hack. Then, they blackmail targeted individuals – forcing them to hand over their corporate credentials, provide information on internal systems or distribute spear-phishing attacks on their behalf.
- Recruiting willing insiders through underground message boards or through the services of “underground recruiters.” These insiders receive pay for their services and may have to identify co-workers for the criminals to proposition or blackmail.
Blackmailing grew in popularity following recent online data breaches, including the Ashley Madison leak, as these provide attackers with material they can use to threaten or embarrass individuals. In fact, data-leak related extortion has now become so widespread that the FBI issued a Public Service Announcement on June 1, warning consumers of the risk and its potential impact.
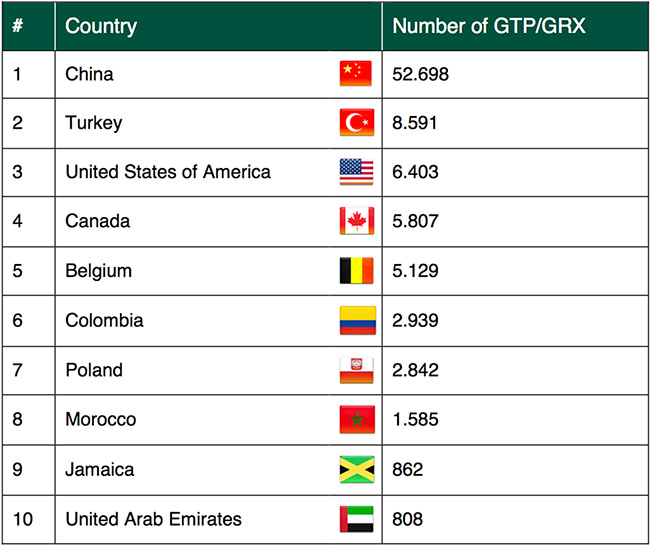
Top 10 countries with GTP/GRX ports exposed to Internet access
Demand for insiders
According to Kaspersky Lab researchers, if an attack on a cellular service provider is planned, criminals will seek out employees who can provide fast track access to subscriber and company data or SIM card duplication/illegal reissuing. If the target is an Internet service provider, the attackers will try to identify the employees who can enable network mapping and man-in-the-middle attacks.
However, insider threats can take all forms. Kaspersky Lab researchers noted two non-typical examples, one of which involved a rogue telecom employee leaking 70 million prison inmate calls, many of which breached client-attorney privilege. In another example, on a popular DarkNet forum, an SMS center support engineer was advertising their ability to intercept messages containing OTP (One-Time Passwords) for the two-step authentication required to login to customer accounts at a popular fintech company.
“The human factor is often the weakest link in corporate IT security,” said Denis Gorchakov, security expert, Kaspersky Lab. “Technology alone is rarely enough to completely protect the organization in world where attackers don’t hesitate to exploit insider vulnerability. Companies can start by looking at themselves the way an attacker would. If vacancies carrying your company name, or some of your data, start appearing on underground message boards, then somebody, somewhere has you in their sights. And the sooner you know about it the better you can prepare.”