Targeted campaign uses infostealer to hijack Facebook Business accounts
WithSecure researchers have discovered an ongoing operation, dubbed “DUCKTAIL”, that targets individuals and organizations operating on Facebook’s Ads and Business platform.
Based upon analysis and gathered data, the company has high confidence that the operation is conducted by a Vietnamese threat actor. The chain of evidence suggests that the threat actor’s motives are financially driven.
The campaign and malware
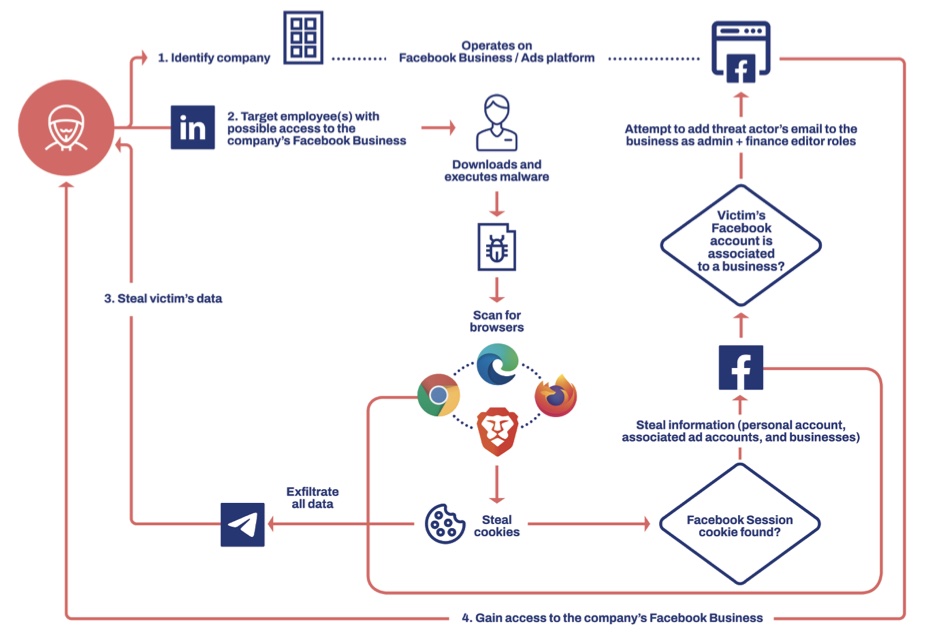
DUCKTAIL’s operations utilize an infostealer malware component that includes functionality specifically designed to hijack Facebook Business accounts. This is the first instance of such functionality that WithSecure is aware of, and it separates DUCKTAIL from earlier Facebook-centric malware operations. The infostealer is designed to steal browser cookies and take advantage of authenticated Facebook sessions to steal information from the victim’s Facebook account and ultimately hijack any Facebook Business account to which the victim has sufficient access.
The company has found DUCKTAIL scouting for and phishing its targets via LinkedIn, where it selects users likely to have high-level access to a Facebook Business account, especially those with admin privileges.
“We believe that the DUCKTAIL operators carefully select a small number of targets to increase their chances of success and remain unnoticed. We have observed individuals with managerial, digital marketing, digital media, and human resources roles in companies to have been targeted,” said Mohammad Kazem Hassan Nejad, Researcher for WithSecure Intelligence.
Initially discovered as an unknown malware earlier this year, WithSecure started tracking and analyzing the operation and found that the threat actor had been developing and distributing the DUCKTAIL-linked malware since the second half of 2021. The DUCKTAIL operation has since continued to update and push out the malware in an attempt to improve its ability to bypass existing or new Facebook security features alongside other implemented features.
Social media accounts wanted for malicious purposes
While WithSecure has detections in place for endpoint protection platforms (EPP) and endpoint detection and response (EDR) solutions such as static and behavioural detection signatures, and detections for multiple stages of the attack lifecycle, Mohammad Kazem Hassan Nejad also adds that vigilance and alertness are key to avoiding becoming a victim.
“Many spear phishing campaigns target users on LinkedIn. If you are in a role that has admin access to corporate social media accounts, it is important to exercise caution when interacting with others on social media platforms, especially when dealing with attachments or links sent from individuals you are unfamiliar with,” he noted.
The popularity of social networks and media platforms remains on the rise. Unfortunately, this attracts cybercriminals to find ways of abusing these platforms for their own gains, such as using them for malware distribution, theft, disinformation campaigns, and fraud. Malware targeting social platforms such as Facebook has thus far been relatively uncommon due to the security mechanisms implemented by the platforms. Still, the wide outreach and user base make it an interesting attack vector for threat actors to abuse.
WithSecure had shared its research prior to release with Facebook’s parent company Meta. A detailed report about DUCKTAIL’s operation and an overview of the attack using the MITRE framework can be found at here.