Targeted attacks focus on nationalistic and economic cyberterrorism
When it comes to dangerous Web threats, the only constant is change and gone are the days of predictable attack vectors. Instead, modern blended threats such as Aurora, Stuxnet, and Zeus infiltrate organizations through a variety of coordinated tactics, usually a combination of two or more.

Phishing, compromised websites, and social networking are carefully coordinated to steal confidential data, because in the world of cybercrime, content equals cash. And, as a new Websense report illustrates, the latest tactics have now moved to a political and nationalistic stage.
Cybercriminals and their blended attacks are having a field day taking advantage of security gaps left open by legacy technologies like firewalls, anti-virus, and simple URL blockers.
The report showcases how in today’s threat landscape, legacy defenses simply don’t work. We all have anti-virus, firewalls and proxies installed, but that isn’t enough.
Threats are no longer binary files delivered in attachments, they are script-based attacks and they are embedded in rich media like Flash. And many spread rapidly on the social Web. Reputation filters provide zero security for threats delivered via top “legitimate” websites like Google, Facebook, and YouTube, where 80 percent of Web traffic goes.
Cybercriminals know that legacy technology simply looks for known information (signatures) or reputation of previously identified threats, which is why they are so successful at exploiting existing defenses. Most of today’s blended attacks are considered “zero-day,” in that they have not been previously identified. They are ever-evolving and pre-tested by cybercriminals on common anti-virus products before they are released. These threats sail through firewalls and open channels.
In 2010, cybercriminals adapted their strategies to address the social websites and sites with dynamic user-generated content. Attacks are now more blended, sophisticated, and targeted. Many of these attacks use new tricks and methods of delivery.
cript-based attacks, blended email campaigns, and SEO poisoning were all common in 2010. Even the most easily detected threats and botnets were successfully repurposed with variations that often allow them to slip through outdated defenses. The majority of attacks in 2010 focused on the same thing: stealing data.
Significant findings from the Websense 2010 Threat Report affirm that while broad threats continue, focused, targeted attacks are on the rise. Findings include:
- 111.4 percent increase in the number of malicious websites from 2009 to 2010
- 79.9 percent of websites with malicious code were legitimate sites that have been compromised
- 52 percent of data-stealing attacks were conducted over the Web
- 34 percent of malicious Web/HTTP attacks included data-stealing code
- 89.9 percent of all unwanted emails in circulation during this period contained links to spam sites and/or malicious websites
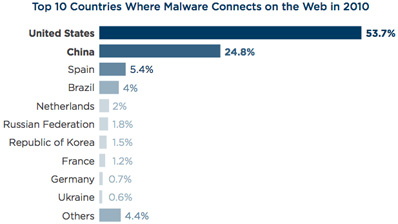
- The United States and China continued to be the top two countries hosting crimeware and receiving stolen data during 2010; the Netherlands has found its way into the top five
- Searching for breaking news represented a higher risk (22.4 percent) than searching for objectionable content (21.8 percent)
- 23 percent of real-time search results on entertainment lead to a malicious link
- 40 percent of all Facebook status updates have links and 10 percent of those links are either spam or malicious.